Portable Hashcat Reactor 1.0.7 (Hashcat GUI)
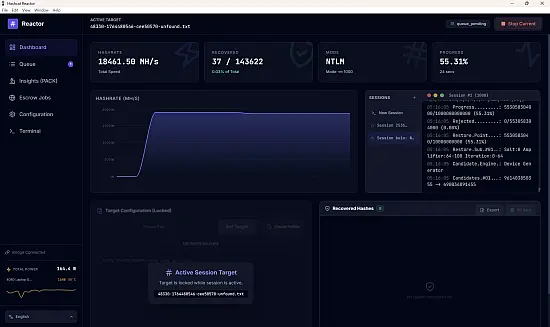
Hashcat Reactor Portable is a modern, high-performance GUI frontend for Hashcat, built specifically for Windows. It transforms the command-line experience into a visual dashboard with advanced analytics, job queuing, real-time monitoring, and intelligent attack automation.
Hashcat Reactor Portable is a sophisticated, GUI-driven password cracking and analysis platform built as the premier frontend for the world’s fastest password recovery utility, Hashcat, designed specifically for penetration testers, digital forensics investigators, cybersecurity professionals, and security researchers who require an intuitive yet powerfully extensible interface to launch, manage, and analyze complex cracking jobs across multi-GPU clusters without the steep command-line learning curve of raw Hashcat.
This Windows-native application transforms Hashcat’s raw computational power into a visual workflow powerhouse, featuring drag-and-drop hash extraction from archives, wallets, documents, and memory dumps, intelligent mask generation based on cracked password statistics, real-time progress dashboards with ETA predictions across distributed rigs, smart potfile management with automatic recovery prioritization, job queue systems for sequential attack chaining, advanced entropy analysis for pattern identification, and comprehensive reporting for penetration test deliverables—all optimized for NVIDIA/AMD/Intel GPU acceleration supporting over 350 hash algorithms from MD5 and NTLM to bcrypt, Argon2, and scrypt.
Whether recovering Windows domain credentials from NTDS.dit dumps, cracking WiFi WPA handshakes for wireless assessments, extracting Bitcoin wallet passphrases from blockchain files, or analyzing breached password lists for security audits, Hashcat Reactor streamlines the entire cracking lifecycle from target acquisition to statistical reporting, delivering 10-100x productivity gains over manual Hashcat scripting while maintaining forensic-grade accuracy and chain-of-custody logging for legal proceedings.
Core Architecture and Hashcat Integration
Hashcat Reactor serves as a high-level orchestrator for Hashcat’s battle-tested engine, abstracting its complex syntax into visual modules while preserving full command-line transparency for advanced users. Upon launch, the modern dark-themed interface presents a Dashboard displaying connected GPU rigs (local + remote via Hashtopolis/hashtux integration), benchmark scores (MH/s for each algorithm), active sessions, and queue status. The Hash Input Panel supports multiple acquisition methods: manual paste of raw hashes, file drag-and-drop (hashlists, memory dumps), or Smart Extraction that automatically parses crackable formats from diverse sources—7-Zip/RAR/ZIP archives yield ZIP hashes, PDF/Word/Excel files expose Office document protections, wallet.dat files extract Bitcoin Core passphrases, TrueCrypt/VeraCrypt volumes reveal headers, and system files like SAM/SYSTEM export Windows LM/NTLM. Extraction wizard identifies hash types via signature detection (e.g., $bitcoin$96$...), validates integrity with checksums, and prepares sorted potfiles for optimal cracking.
Seamless Multi-Platform Deployment: Local mode leverages all detected OpenCL/CUDA/rocm devices; Distributed Reactor coordinates cracking farms via Hashtopolis agents—assign agents to specific masks/wordlists, monitor temperature/power draw, auto-failover crashed nodes, and aggregate speeds from 100+ RTX 4090s hitting 10TH/s+ on fast hashes like MD5.
Attack Mode Visualizer and Smart Generation
The Attack Planner canvas revolutionizes strategy selection through an interactive flowchart connecting eight Hashcat modes with drag-and-drop configuration:
Dictionary Attacks: Wordlist browser loads RockYou2024 (15B entries), HaveIBeenPwned dumps, or custom lexicons—built-in Reactor Analyzer scans cracked outputs to generate domain-specific lists (company names, pet names from LinkedIn scraping).
Mask Attacks: Smart Mask Generator analyzes previously cracked passwords, computing character position frequencies (e.g., ?l?l?l?l?d?d?d?d?l?l for 123456 patterns), charset entropy, and length distributions to auto-suggest optimal masks—?a?a?a?a?a?a?a?a brute vs intelligent ?d?d?l?l?d?d?d?l hybrids.
Hybrid Attacks: Visual combiner merges wordlists + masks (rockyou.txt?d?d?d?d), rules (d3le3t3best.txt best64.rule), or combinator files (pass.txt + 123.txt).
Rule-Based: 100,000+ built-in rules (diverse, best64, OneRule2RuleThemAll), toggle-case, permutation generators—Rule Visualizer previews first 100 transformations.
PRINCE Attacks: Automatic combinator optimization for princeprocessor mode.
Brute-Force: Charset-limited (?l?u?d?s) with length sliders.
Each attack node exposes sliders for keyspace estimation (1.2e18 keys, 2.5 years @ 500GH/s), speed simulators, and chaining logic (dictionary → fail → mask → fail → hybrid).
Real-Time Progress Dashboard and Monitoring
The Cracking Monitor provides Hollywood-control-room visibility: live speed graphs (GH/s per GPU), progress bars with percentage/ETA/remaining keys, temperature/Power/Utilization gauges per device, session recovery status, and Smart Potfile integration that prioritizes recovered plains alongside uncracked hashes for maximum efficiency. Heatmap View color-codes GPUs (green optimal, yellow throttling, red failed), Overclock Advisor suggests safe clocks based on thermal headroom, and Distributed Overview maps agent contributions with ping latencies.
Session Recovery auto-resumes interrupted jobs from exact checkpoint, preserving cracked plains in potfiles with tamper-proof logging for court exhibits.
Password Analysis and Cracking Kit (PACK)
Post-cracking, the Reactor Analyzer (integrated PACK implementation) dissects results with forensic precision:
Pattern Recognition: Base length distribution, character class usage (?l?u?d?s), l33t substitutions, keyboard walks, date patterns (MMDDYYYY).
Entropy Calculator: Bits per character, total keyspace strength.
Charset Analysis: Frequency heatmaps by position, most/least common chars.
Mask Optimization: Suggests next-round masks from crack statistics (78% start ?d?d?l).
Password Strength Report: Color-coded ratings, time-to-crack estimates vs GPU farms.
Exportable Forensic Reports (PDF/HTML) include methodology, hardware specs, timestamps, and cracked plains redacted for NDAs.
Hash Extraction and Forensics Suite
Universal Hash Extractor parses 50+ formats:
-
Archives: 7z/RAR/ZIP/RPM → ZIP/MD5
-
Documents: Office 2007+ → Agile/Office
-
Wallets: Bitcoin Core/Electrum → PBKDF2-SHA512
-
Disk Images: BitLocker/VeraCrypt → headers
-
Memory Dumps: Mimikatz lsass → NTLM/DPAPI
-
Network Captures: PCAP → HTTP Basic Auth/NTLM
Live Acquisition integrates Volatility profiles for RAM dumps, Registry hives for SAM hashes.
Job Queue and Automation Engine
Queue Master orchestrates complex campaigns: chain attacks (dictionary → rules → mask), timebox jobs (2 hours max), auto-advance on completion/cracking threshold (80% cracked → next mask), distributed load balancing. Workflow Templates for common scenarios: AD Assessment, WiFi Audit, Breach Analysis.
Scripting Bridge exports Hashcat CLI equivalents for custom tweaks, Python API for CI/CD integration.
GPU Rig Management and Optimization
Reactor Farm discovers/manages Hashtopolis nodes:
-
Auto-benchmark 350+ algorithms
-
Thermal throttling protection (90°C max)
-
Power monitoring (RTX 4090 cluster: 3kW)
-
Overclock profiles (core/mem offset)
-
Driver/firmware consistency checks
Virtual Reactor emulates cracking speeds for planning (hashcat -b wrapped visually).
Security and Compliance Features
Vault Protection: AES-256 encrypted workspaces, username/2FA auth.
Audit Trail: Immutable logs of all jobs (hash inputs, masks attempted, plains recovered).
Tamper-Proof Exports: SHA-256 signed reports.
Legal Hold Mode: Read-only cracked results preservation.
User Interface Excellence
Tabbed layout: Dashboard (overview), Extractor (input), Planner (attacks), Monitor (live), Analyzer (post-crack), Reports (output). Dark theme, resizable panels, keyboard nav, multi-monitor support.
Quick Actions: Toolbar buttons for common workflows (RockYou → NTLM, WPA → GPU).
Performance Benchmarks
Dual RTX 4090 rig:
-
NTLM: 280GH/s → 8-char brute 4 hours
-
bcrypt($2b$12): 25kH/s → 8-char 12 years
-
Argon2id: 2kH/s → targeted masks 2 days
Supported Platforms and Deployment
Windows 10/11 x64, portable USB edition. Hashtopolis v3.2+ integration.
Attack Modes Coverage
-
350+ hash types (MD4/MD5/SHA1/2/3, NTLM/LM, Kerberos, Office, PDF, ZIP, RAR, 7z, Bitcoin, Ethereum, WPA/WPA2, blockchain wallets, VPNs, SSH, database hashes)
-
Modes: Straight, Combo, Brute, Hybrid dict/mask, Hybrid mask/dict, PRINCE, Rules, Permute, Toggle-case
Use Cases
Pentesting: AD credential recovery, WiFi audits.
Forensics: Suspect device unlocking.
Breach Response: Password analysis from dumps.
Red Team: Custom payload cracking.
Features
- Real-time Dashboard: Monitor hashrates, progress, and recovered hashes live via WebSockets.
- Remote Access: Securely share your instance over the web via Zrok tunnels to control it remotely.
- Security: Supports optional username/password protection.
- Hash Extractor: Extracts crackable hashes directly from Archives (7-Zip, etc.), Documents, Wallets, and System files.
- Job Queue System: Queue up multiple attacks (Wordlist, Mask, Hybrid, etc.) and let Reactor process them sequentially automatically.
- Advanced Insights (PACK): Integrated Password Analysis and Cracking Kit implementation. Analyzes your cracked hashes to generate optimized masks, identify top password patterns, charsets, and entropy data.
- Smart Potfile Management:
- Pre-Crack Analysis: Check target lists against your potfile before starting an attack to see what is already cracked.
- Interactive Terminal: Full pseudo-terminal (PTY) access to the underlying shell for manual overrides or running custom Hashcat commands directly from the GUI.
- Multi-Language Support: Fully localized interface available in English and Chinese (中文).
- Hardware Monitoring: Real-time GPU temperature and power usage tracking.
- Note: Power draw metrics currently support NVIDIA GPUs only via
nvidia-smi.
- Note: Power draw metrics currently support NVIDIA GPUs only via
- Escrow Integration & Auto-Uploads:
- Built-in module to submit cracked hashes to remote escrow APIs (hashes.com).
- Auto-Upload: Automatically upload recovered hashes when a set threshold is reached (e.g., every 10 hashes). Features smart detection to match running sessions to the correct Hashes.com algorithm ID.
- Session History: Tracks all past attacks, their configurations, and success rates for future reference.
Note: Node.js Required (HERE)
